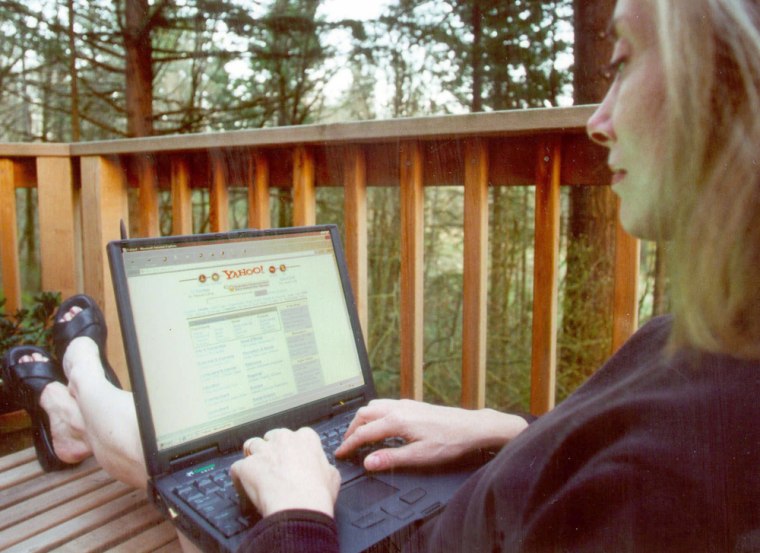
For many people, it’s not the appeal of working in their pajamas that convinces them to make the leap; or the chance to sleep in a little later and still be at work on time; or even the chance to avoid sitting in traffic every morning and evening. No, telecommuting’s big attraction is often the simple joy of trading in your cubicle for your backyard garden. When you work from home, no one knows if you are typing e-mail while getting a tan on your deck, or grilling hamburgers on the barbecue.
It's home wireless networks that make these visions come true. After all, if you are becoming untethered from the office, you might as well be untethered at home, too.
Ask anyone who has wandered around their home with their laptop, from TV to fridge to front yard, and not missed an e-mail. It’s liberating. For both you, and unfortunately, your data.
You knew there was a catch, didn’t you? If you can walk around your house picking your files out of thin air, so can anyone else. In fact, the snooper doesn’t even have to be in your house. The little radio station you install in your home to beam the Internet around the place doesn’t understand property lines. So when you go wireless, you should know that neighbors several houses away can see what you are doing. Yes, they can literally pick your data right out of the air.
And the truth is, experts believe most home wireless networks are left casually insecure like this, with workers unknowingly sending this newly “liberated” data up and down the block all day long.
“I have a friend that ... can see five of her neighbor’s wireless networks,” said Christopher Thompson, vice president of marketing for Sniffer Technologies, which sells wireless security products.
Consumers may have noticed in recent months that a new line of wireless products based on an improved “G” standard have started popping up in electronics stores around the country. These products, known also by their full name, “802.11G,” zip data around your house twice as fast as the old products.
But don’t be confused: there’s nothing in the G-standard that makes these devices any more secure than the old “802.11B” wireless. So even with the latest equipment, there’s still a lot of work that needs to be done before you should work wirelessly at home.
Lose your pajamas license
That’s because broadcasting your e-mails to mom is one thing; telecommuters broadcasting company secrets down the block is quite another. It’s enough to quickly get your license to work in your pajamas revoked. But the good news is, there’s a lot you can do to severely decrease the odds that you’ll be snooped.
Protecting your home wireless network is a good news/bad news story. First, the bad news. Most experts will tell you that there’s practically no way to make it completely safe from prying eyes. Even the most widely available encryption technology has been cracked.
But the good news is there are several simple steps that home wireless users can take which greatly reduce the likelihood that someone will snoop your data. Four, to be exact.
Don’t call attention to yourself
Change your name
Scramble your data
Telecommute through a tunnel
1. Don't call attention to yourself
Each wireless device has a name, called a Service Set Identifier, or SSID. Any device that tries to hop onto the wireless party line must know this name. By default, most networks broadcast this name to make connecting easier — the equivalent of saying to the world “here’s my front door, it’s probably open if you want to try it.” That’s a good idea if you are Starbucks, and you want customers to breeze in and out of your network. It’s a bad idea if you don’t want Victor, the voyeur next door, to read your e-mail. Turn off the broadcast SSID function and you’ve won 25 percent of the battle. It means a hacker will have to guess your network’s name to get in.
2. Change your name
Now, make guessing that name much harder — change it. Wireless network vendors ship their products with SSID names set to obvious defaults. For example, the popular LINKSYS product uses the name “linksys” as its SSID, until it’s changed. Hackers know this, and wander round town using programs with names like “Netstumbler” to see who’s leaving their data up for grabs. If they detect you’re using a Linksys card, they may attempt to connect to your network by trying the linksys SSID. Take another moment to change the default, and you’re halfway there. If you change your SSID every few months, you’re more than half way home.
3. Scramble your data
Thanks to days gone by when the various brands of wireless devices didn’t play nice with each other, manufacturers decided it was best to turn off encryption when their products were sold. That solved some of the incompatibility problems, but it created the big problem we have today — namely, that when Victor the neighbor hops onto your network, he can read your e-mail because it flies around your house in plain text. But nearly all devices have an option to scramble the data using an encryption tool called WEP — Wired Equivalent Privacy. WEP works, and will almost certainly make Victor give up his casual digital voyeurism.
But the bad news is, WEP isn’t fool proof. If Victor is a serious hacker, with the right motivation, the right tools, and free time on his hands, he can decipher your encryption key and unscramble your e-mail.
That should certainly give wireless users pause, but the news isn’t as bad as it sounds at first, says Nigel Ballard, Director of Wireless for Matrix Networks in Portland, Ore.
“It takes an extremely determined, socially maladjusted individual to sit outside your house for hours on end,” to decipher the data, said Nigel Ballard, Director of Wireless for Matrix Networks in Portland Ore. “If he’s parked outside your house, there’s so little traffic going over your access point, he may have to sit out there solidly for a day and a half. And if he wants to see your e-mails that badly, I suggest he just break a window.”
That’s why using WEP only gets you three-quarters of the way there.
4. Telecommute through a tunnel
The fourth step, the one that will require you to get help from the office, is to use a Virtual Private Network, or VPN. A VPN creates a digital “tunnel” between your backyard laptop and your office. It’s essentially a special piece of software that’s used to log on to the office network. But the tunnel is fortified with better encryption than WEP — so much better, that most experts think it’s nearly foolproof. The good news is the tunnel that protects data as it travels over the phone line and the Internet to your office also protects it as it flies around the airwaves near your home. When you are sending traffic through the tunnel, it’s nearly certain a hacker can’t sniff it.
“The good thing about a VPN is that it will secure the entire communication path — the wireless link and all the hops across the Internet, right up to the network that you’re remoting into,” said Scott Culp, Program Manager for Security Strategies at Microsoft. All versions of WindowsXP include the desktop software required to connect a virtual private network.
But there is a caveat — the tunnel only protects data that’s destined for the office. Even if you are logged on to the VPN, when you send files around your home network, they are not protected by the tunnel. So for example, when you download a secret company merger document off a server, and look at it on your laptop in at the edge of your swimming pool, the data is protected. But if you beam it to your printer in your home office, it’s not — unless you have followed steps one, two and three.
An exclusive list
There is one additional step Ballard suggested, but it’s only available with some wireless devices. Every computer device with networking capabilities has a unique MAC address, a bit like a serial number. Some wireless devices allow users to create an “authorize MAC address table” which means only devices with these specific serial numbers are allowed on the network. Hackers can “spoof” MAC addresses, effectively telling their computer to impersonate one of yours. But to do so, they will have to somehow learn your device’s serial number — another serious hurdle to overcome.
Investment bankers: Don't go wireless
Still, given all those caveats, most experts will concede that there’s no way to promise 100 percent security for a wireless network. Like any security plan, protecting a home wireless network is more about improving the odds that you’ll be safe than it is about slamming the door around Fort Knox. And in fact, many federal government departments don’t allow wireless networks because of the various security concerns.
“If I was an investment banker working on a corporate merger from home, I probably wouldn’t use a wireless home network,” Thompson said. “You take appropriate steps based on what you are doing.” For most home users, following the four steps above will provide a sufficient level of security, he said.
Reasons for hope
But for those who are really worried about snoopers, there is hope.
Wireless products with an updated encryption scheme, called Wi-Fi Protected Access (WPA), are just now trickling into the marketplace, according to Brian Grimm, spokesman for the Wi-Fi Alliance. As of Aug. 31, all new Wi-Fi products must support WPA to be certified by the alliance — and already about 50 products are.
Hackers haven’t cracked the more complex WPA encryption, Grimm said, so wireless networks using it will be much safer. Most wireless products sold in stores today still include the older WEP, but they will be replaced over time with WPA devices, he said.
Consumers can look on the Wi-Fi Alliance Web site or on compatibility labels at retail stores to see which encryption scheme is included in the wireless device they are buying.
This story was originally published Sept. 29, 2003.