A company developing encryption-based software for secure electronic voting has itself become the victim of a computer break-in, the company’s top executive told MSNBC.com. Federal authorities have confirmed that the incident is under investigation.
The intrusion into Bellevue-based VoteHere’s corporate network occurred in October, said Jim Adler, VoteHere’s founder, president and chief executive officer. No suspects have yet been named, but Adler said his company, in cooperation with investigators, had developed substantial information about the source of the intrusion over the past two months.
“We feel that it may have been politically motivated,” Adler said.
Adler’s revelation came amid a deepening debate over e-voting and its vulnerability to election fraud — and a controversy over surreptitious methods to get information about how e-voting software works.
The politics of paperless voting
The best-known case arose earlier this year, when e-voting critics claimed that they had obtained the code for Diebold Election Systems’ software from the company’s corporate network. Researchers analyzed that code to claim that Diebold’s software was insufficiently secure against fraud — fueling a campaign to require that e-voting systems print out paper ballot receipts as well, as part of a voter verification system.
In the past two months, California and Nevada state officials said they would put such requirements into effect by mid-2006. Other states are looking into similar measures, and three pieces of federal legislation relating to e-voting verification have been introduced in Congress (H.R.2239 and its companion S.1980, as well as S.1986).
Adler said his company has “seen some connection” between the criticism of e-voting systems and October’s computer break-in, but he declined to go into specifics.
“I don’t want to necessarily politicize this,” he said. “This is just a crime.”
Investigators monitored intruder
He said the intruder took advantage of a network security hole “that we were a patch behind on.” While gaining entry, the intruder set off an electronic “trip wire” that alerted VoteHere, he said. Federal authorities were immediately told of the break-in, Adler said, and the intruder’s activities were monitored as part of the investigation. Then access was blocked.
The investigation is being conducted by the Washington Cyber Task Force, a Seattle-based effort that involves the FBI, the U.S. Secret Service and local law-enforcement officials. Spokesmen for the FBI and the Secret Service confirmed to MSNBC.com that an investigation was under way but declined to comment further.
Adler said he was discussing the incident even though the investigation is not finished because “we believe that others in the election industry should be aware of it.” He declined to say what kind of information the intruder might have taken, but emphasized that the break-in did not compromise the integrity of VoteHere’s software or any voting results.
What the software does
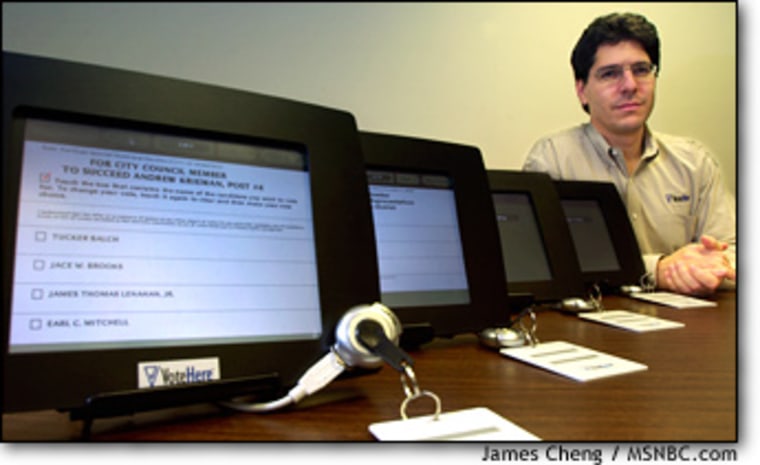
VoteHere’s products are designed to encrypt ballots in such a way that voters can make sure their votes have been counted correctly, even after the election, while at the same time keeping those ballots secret and safe from fraud. Such software would be used as a paperless voter verification method in systems marketed by other companies — say, by Diebold or one of its competitors.
VoteHere’s remote-voting technology has been tested in British local elections and nongovernmental tallies such as the Country Music Awards. The company also has partnered with Sequoia Voting Systems for distribution of its paperless ballot verification system, but the software has not yet been deployed under that deal.
Adler said encrypted voting results are stored on VoteHere's network, but he said "there is no evidence that any election was compromised."
Secrets in the system
Some e-voting companies contend that their software code is proprietary and must remain secret, leading critics to charge that voters would be entrusting their ballots to a “black box.” But when it came to the VoteHere break-in, Adler said the software source code wasn’t his primary worry, since his company eventually would disclose the code anyway.
However, he added, “there are some things that are proprietary, like people’s salaries and their HR [human relations] history.”
“Everything isn’t the ‘Pentagon Papers,’” he said, referring to the famous case involving leaked Pentagon documents on the Vietnam War. “The ends do not justify the means, in most cases.”
The mere fact that someone was able to gain unauthorized access to an e-voting company’s computer network might lead some to question the security of e-voting. But Adler said cryptographic voting systems are able to weather such intrusions.
“It’s true that systems would always be compromised,” he said. “The point is, you want to know about it. ... If you can detect when those things happen, that’s what’s vitally important. Any ballots that get compromised will get detected, and that’s what’s crucial.”