The digital footprints we leave behind as we go about our Internet-browsing, cellphone-calling, app-using lives may be revealing more about us than we realize — and opening us up to some surprising risks.
The potential pitfalls were highlighted recently when an Australian college student discovered that maps released by the fitness-tracking app Strava could be used to identify U.S. military bases.
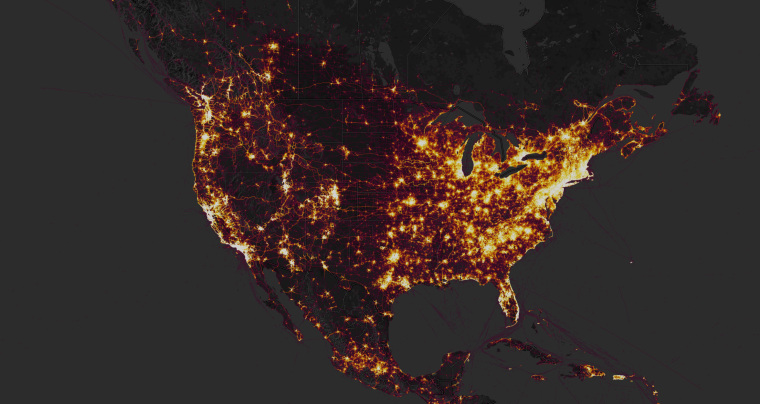
The company had used anonymized GPS data from its users’ jogging and cycling routes to create a global “heat map” of activity. But because the app is popular with military personnel, the maps revealed the locations of bases as well as sensitive details about their layouts and even service members’ routines.
It was even possible to identify individual military personnel by uploading routes to Strava’s website to see who had the fastest times at these locations.
"It really demonstrates our inability to comprehend the consequences of what we're sharing,” says Dr. Mani Srivastava, a UCLA professor with a special interest in security and privacy issues arising from the use of mobile devices.
Revealing your location
Military personnel aren’t the only ones at risk. Unless you opt out of publicly sharing your location data, other Strava users who exercise in the same area can pull up your profile details and see when and where you’re working out. That opens up the possibility that someone could find you during a workout — and that burglars might be able to tell when you’re away from home.
Even if you don’t use a fitness tracker, you may be unwittingly revealing your location to others.
Twitter lets users stamp tweets with a location, and researchers at MIT and Oxford University showed in 2016 that even non-experts could use a day’s worth of tweets to identify someone’s home with 65 percent accuracy.
Facebook also allows users to “check-in” to locations, and SnapChat’s SnapMap function broadcasts your location each time you open the app. Both reveal the information only to your friend list, but security researchers showed in 2011 that one-fifth of Facebook users accepted friend requests from strangers.
In a 2011 survey of 50 convicted burglars in the U.K., four fifths said thieves use social media to case their targets. Three burglars robbed at least 18 homes in New Hampshire in 2010 after checking Facebook for people announcing they weren’t home.
Even when our data isn’t public, we may be sharing more than we realize. Location data tracked by smartphone apps can reveal our shopping habits and how and where we drive, as well as which place of worship we visit, says Srivastava, while motion sensors in fitness-tracking wristbands can show everything from sleep patterns to hand movements that suggest we’re smoking or eating.
In his own house, Srivastava has an internet-connected thermostat that tracks people from room to room to help optimize the settings. “Maybe they could tell I’m a late-night eater because I spent some time in the kitchen at 1 a.m.,” he says.
Who wants your data?
Personal data is valuable to advertisers, and some tech companies’ business models rely on harvesting it. “Many services are only available with your data as your currency,” says Srivastava.
Digital assistants like Amazon Echo and Google Home, which record voice data when users speak to them, could prove particularly intrusive. Dr. Joseph Turow, a University of Pennsylvania professor who specializes in marketing and privacy, says Amazon's privacy policy gives it wide latitude in determining how it will use user data.
"How they build that into their model of who you are I don't know,” he says, “but I don't think most people who have Echoes understand it’s certainly a possibility.”
These profiles can be turned against consumers. In 2012, online travel agency Orbitz acknowledged that it showed Apple Mac users different, often more expensive, options compared to Microsoft Windows users — because data showed Mac users were bigger spenders.
A 2012 Wall Street Journal investigation found that online retailers adjusted prices based on users’ browsing history and location. Displayed prices were higher in areas with little competition from brick-and-mortar stores, which often overlapped with rural and poor areas.
British car insurer Admiral even announced plans in 2016 to assess customer’s personalities by analyzing their Facebook posts, though Facebook forced them to scrap the scheme. It would have denied discounts to motorists whose posts suggested they might be comparatively reckless behind the wheel.
Social credit scores
Emerging “social credit scores” in China may be a harbinger of where this kind of profiling might lead, says Turow.
Sesame Credit combines credit history, shopping habits, and social media data to assign consumers a “trustworthiness” score that governs their access to loans and fast-track visas as well as VIP treatment at hotels. A government-run system scheduled to go online by 2020 would go further, giving users with low scores slower internet speeds, restricted travel, reduced employment opportunities, and limited access to insurance and loans.
"That may seem absurd to us,” says Turow. "But the distance between social credit scores and behavioral activity tracking that today's marketers use is not necessarily all that large.”
Want to do more to limit your digital footprint and plug as many data leaks as possible? Slate’s Futurography project has useful tips. Both Apple iOS and Android version 6.0 allow you to switch off apps’ access to data streams like location (check the privacy settings). Privacy-protecting apps like Signal can also help by encrypting text and voice calls. And DuckDuckGo is one search engine that doesn’t collect user data.
Experts say you should also delete apps you don’t use.

