Well, that didn't take long.
On Sunday, less than two days after the iPhone 5S went on sale, a German hacker collective became the first to claim victory over the gadget's much-buzzed-about Touch ID fingerprint security system. And they did it pretty much the same way Bane's flunkies breached the biometric passcode on Bruce Wayne's stock exchange account in "The Dark Knight Rises," — using a copy of Batman's fingerprints (created by Catwoman after she did some light dusting around Wayne Manor).
Even before the Chaos Computer Club, one of the largest and well-known hacker collectives, crowed victory via the tried-and-true "fake finger" method, Apple's first foray into biometric security wasn't getting a lot of respect. Amid concerns over privacy — Sen. Al Franken, D-Minn., asked if Apple might share stored fingerprints with third parties or the government, the way tech companies do with other customer info — and hacking, the jokes kicked in. A cat's paw, a nipple and a crowd-sourced bounty to the first person to hack Touch ID are likely just the beginning of a running gag at Apple's expense.
"Yes!" declares the IsTouchIDHackedYet.com single-service home page. "The Chaos Computer Club in Germany may have done it! Awaiting video showing them lifting a print (like from a beer mug) and using it to unlock the phone. If so, they'll win ..." a couple thousand dollars in crowd-sourced cash and BitCoin, "a dirty sex book," a bottle of Bulleit Bourbon and other offers of alcohol and miscellany. The contest launched even before the iPhone 5S went on sale.
And, well, if you want to get technical, a "fake finger" isn't a hack (seeing as no software was breached), semantics sticklers are quick to point out. "To its credit, Chaos Computer Club isn't calling the spoof a hack, but that isn't stopping it from being widely misreported, thanks in part to the sloppy title on the YouTube video," iMore's Peter Cohen writes.
Indeed, like Catwoman, Chaos Computer Club created its "fake finger" by first dusting fingerprint fat residue —the kind of fat residue fingerprint you (or Catwoman) might find on an iPhone 5S' Touch ID button thingy. (Hey!) According to a post on the group's website, the hackers then followed the same methods CCC first posted in 2004, took the fingerprint's photo, printed it out, created a mold, and used the bogus biometric to opened the iPhone.
If you want to be a stickler, the iPhone-opening cat and the guy who used his nipple to fool Touch ID didn't "hack" the iPhone 5S security either, no matter how funny it sounds when written in an awesome tweet:
In a video posted on Japanese site RocketNews, a guy successfully registers the unique ridges and whorls of his nipple on the iPhone 5S's Touch ID sensor, then uses it to open the phone. Not a hack, and not really the most convenient (or socially acceptable) method to open up your iPhone in line at Starbucks. (Think how people freak out about mothers nursing their babies in public. Just because it's an Apple product instead of a baby doesn't make it OK!)
This nipple method was similar to the demonstration by a TechCrunch-conscripted kitty-cat, who was assisted in registering a paw print on the new iPhone 5S, which it then used to unlock the iPhone.
"The cat’s paw worked, and while it encountered more frequent failures than did a fingerprint, it was able to unlock the phone again repeatedly when positioned correctly on the sensor," writes Darrell Etherington. "Note that no other paw pads would unlock the device, and that cats essentially have unique 'fingerprints' just like people, so this doesn't make the Touch ID sensor any less secure."

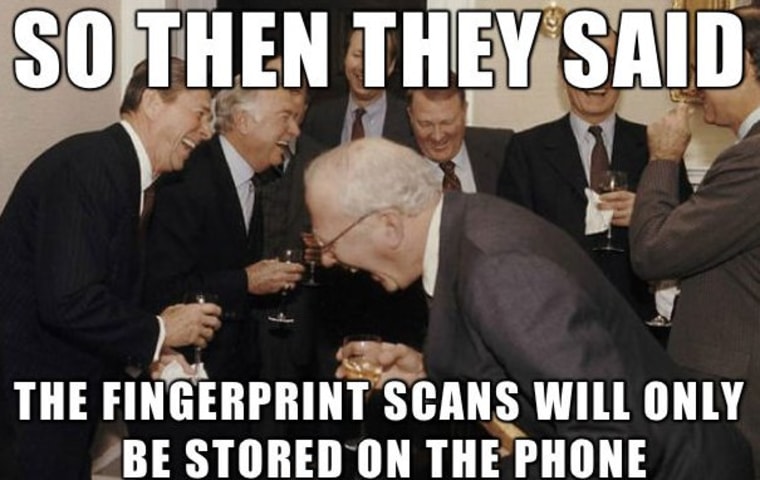
Alongside the Touch ID pranks and cracks, hilarity ensued over the potential privacy threat, with Evil Plotting Raccoon and other image macros making a meme.
"If someone hacks your password, you can change it — as many times as you want, " Sen. Franken writes in his non-humorous letter to Apple CEO Tim Cook. "You can't change your fingerprints. You only have 10 of them."
The Chaos Computer Club takes a more cryptic tone. "Forcing you to give up your (hopefully long) passcode is much harder under most jurisdictions than just casually swiping your phone over your handcuffed hands."
Which sounds easier even than making the fake finger skin used by Chaos Computer Club. "In reality, Apple's sensor has just a higher resolution compared to the sensors so far. So we only needed to ramp up the resolution of our fake," said "Starbug," a hacker quoted on the CCC victory announcement. "As we have said now for more than years, fingerprints should not be used to secure anything. You leave them everywhere, and it is far too easy to make fake fingers out of lifted prints."
Cat paw prints get around too, so that's not a viable solution to securing your Touch ID log-on. Plus, cats are really annoying to carry around to offices, restaurants, bars and other place you might use your phone. Nipples, again, aren't something you'd want to use when you need to access your iPhone in public, but until Internet yucksters come up with a new and ridiculous way to get around fingerprints, that may be your safest bet.
Helen A.S. Popkin goes blah blah blah abut the Internet. Tell her to get a real job on Twitter and/or Facebook.
