FORT MEADE, Md. — Dressed head-to-toe in military fatigues and standing in knee-high grass next to an Army Humvee, Maj. Nikolaus Ziegler held up an unusual smartphone, one equipped with the special security the military wants to deploy in battle.
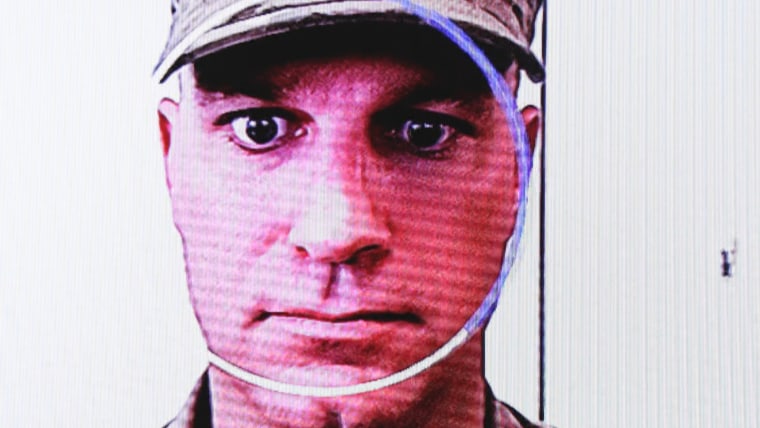
In a few seconds, the prototype smartphone took a scan of his face, measured the height at which he held the phone and analyzed the past hour of his movements. The phone’s security system decided that he was, indeed, Major Ziegler and unlocked itself.
The smartphone is the military's answer to a challenging question: How do you translate the powerful consumer technology of smartphones into something that can be useful and secure on the battlefield?
Ziegler is military deputy at the Emerging Technologies Directorate of the Defense Information Systems Agency (DISA), essentially the information technology branch of the Department of Defense. He explained that soldiers need something better and more secure than today’s smartphones that rely on passwords and fingerprint sensors. The main issue, he said, is that those soldiers often have to hide their faces, their eyes and their fingers.
“If I'm in the field, and I'm going on a military operation, I throw my NBC mask on,” Ziegler said, referring to his gas mask, which protects against nuclear, biological and chemical threats. “Now, my facial recognition is taken off that list.”
So his group decided it needed a more flexible way of identifying a soldier.
"There needs to be additional contextual and biometric factors that allow the device to validate who you are,” he said.
The convenience, portability and usability of smartphones has pushed the military to figure out how to integrate them into the battlefield. The trouble until now has been that consumer-grade phones offer only a certain level of security, and they’re a hassle to unlock in the field.
Ziegler’s new prototype meets a particular set of requirements. It allows graduated levels of security depending on a soldier’s clearance; it improves on a simple passcode or thumbprint for security; and it allows a variety of factors to serve as evidence that the phone’s owner is, indeed, holding the device.
With this new technology, which DISA is calling “Assured Identity,” the phone will watch everything it can about its owner in order to constantly confirm that it’s in the right hands.
But the DOD is in a different position than in previous decades, when companies would compete for lucrative contracts to build new weapons and tools to their specifications.
Ziegler said he was part of a group that asked Apple to build a military version of its first iPhone, with additional features to make it more rugged and more secure. The company refused, he said, citing too small a market opportunity.
Even including every active-duty American soldier, the market for such a device is only a couple of million people. So the DOD is at the mercy of a market now dominated by large tech companies selling variations of the same product to tens or hundreds of millions of people. That makes the DoD a comparatively small customer.
In a reversal of roles, the DOD now hopes to essentially sell some of the technology it’s developing to a manufacturer like Google, Samsung or some other company.
The hope is that a company will then mass-produce phones with similar security features, so that the department can buy them at an affordable price for its personnel. The trouble is that a mass-market version of the technology could be less secure — and more intrusive — than what the DOD has in mind.
“Even if the phones are well secured, allowing the vendor to take the data off the device and store it on their servers would be a source of security risk,” said Riana Pfefferkorn, associate director of surveillance and cybersecurity at Stanford University’s Center for Internet and Society. “Obviously this data, if held by a private vendor, would be a target for hacking by America’s enemies. Plus, careless security practices could lead to a data breach, or the data could be compromised due to an insider threat, such as an employee selling it without authorization.”
In recent years, biometrics have emerged in consumer electronics as an alternative to passwords. Fingerprints and even now face scans have become routine parts of the day-to-day of millions of people who use Apple and Samsung smartphones.
But that technology has also come with fresh privacy concerns about just what happens to biometric information.
The DOD smartphone takes biometric security to a previously unseen level. It combines everything from the places a person habitually visits and their most common connections to Wi-Fi networks to the calls they regularly make, and then combines that data with biometrics like the patterns of their strides to build a “trust score” that keeps the phone unlocked. Ziegler said that within about 100 yards his phone knows who he is from the rhythm of his gait and which pocket he usually uses to carry it.
If another person grabs the phone and walks off, the distinct pattern of his or her walk would change the trust score in just a few strides.
"It's continuously checking things on you,” he said, smiling.
Stephen Wallace, a systems innovation scientist at DISA, argued that the system could make life incredibly convenient even if it were only given to active and retired military personnel.
“My father carries around his V.A. card,” he said. "And when he goes to the hospital, he presents his V.A. card. Well, what if we could get to the point where they don't need that anymore?“
Wallace described a world where biometric factors like a fingerprint and being left-handed, together with the habits of a person’s daily life, don’t just replace passwords, they safeguard every transaction.
The trick, Wallace said, is requiring more security for certain transactions. To allow you to do something high-stakes — like transfer money from a bank account, for instance — Wallace said the phone would need to check multiple factors off the list. A $20 transfer might need only a fingerprint, whereas a $10,000 transfer could require a far greater amount of physical and situational data.
But biometric data, like all digital information, is hackable. Privacy advocates have warned that the faces of people who have posted pictures online are used without permission to train facial recognition programs. When Apple launched its Face ID feature, the company reassured users that any information about a user’s face would stay on the phone — though Reuters found that some developers were able to gain access to facial data. More recently, biometric information from more than 1 million people was found on a publicly accessible database used by a security company.
Wallace said the DISA prototype keeps all of the data on the phone rather than sending it to the cloud, where it might be compromised in a data breach. But that’s the military concept. If “assured identity” were to become a mass-market product, the rules would almost undoubtedly be different, he said.
“Our position going into this was that [the data storage] needs to be done local,” Wallace said. "Because we've seen time and time again where, you know, there have been infiltrations and people's privacy data has been taken. So we really want to be mindful of that.”