In declaring that, "Like other service providers, we are engaged in an arms race with malware distributors," Google has thrown down the gauntlet in the battle against malware distributors, and now it's compiled four years worth of data that shows how its crafty adversaries have continued stealthy efforts to infiltrate lives and wreak havoc.
In a post yesterday on the Google Online Security Blog, Google Security Team members Lucas Ballard and Niels Provos laid out the highlights of the dense report, which "explores the evasive techniques that malware distributors employ" over about 160 million web pages hosted on approximately 8 million sites.
It's an epic struggle that the search engine giant is thoroughly entrenched in, sending out "around 3 million malware warnings to over 400 million users whose browsers implement the Safe Browsing API." The Safe Browsing API enables apps to automatically checks URLs against a constantly updated database of suspected phishing and malware pages. This tool gives developers a weapon to warn users before clicking on links that appear in their site that could lead to malware-infected pages. It can also prevent users from posting links to known phishing pages.
So users benefit, even when they don't see what is happening. The code blocks the triggering mechanism that leads to an attack. But Google has made its defenses visible to users in other ways, with alerts to users about malware infections, flagging websites, and in search results, some sites may be flagged, "This site may be compromised" or This site may harm your computer."
In "Trends in Circumventing Web-Malware Detection," team members focused on "the four most prevalent detections techniques: Virtual Machine honeypots, Browser Emulation honeypots, Classification based on Domain Reputation, and Anti-Virus Engines."
While probably only developers can really make the most of this report, it does also give users insights on how many different ways those with malicious intent are trying daily to take advantage of innocent users.
To try to translate some of this to us ordinary folk: security experts can typically find malware by scrutinizing any new processes to an operating system; by making copies of browsers to pinpoint vulnerabilities; by flagging "domains as malicious weeks before they appear on public blacklists"; and by using more traditional anti-virus scans.
The study confirms the team's hypothesis that "malware authors continue to pursue delivery mechanisms that can confuse different malware detection systems," but that "adopting a multi-pronged approach can improve detection rates."
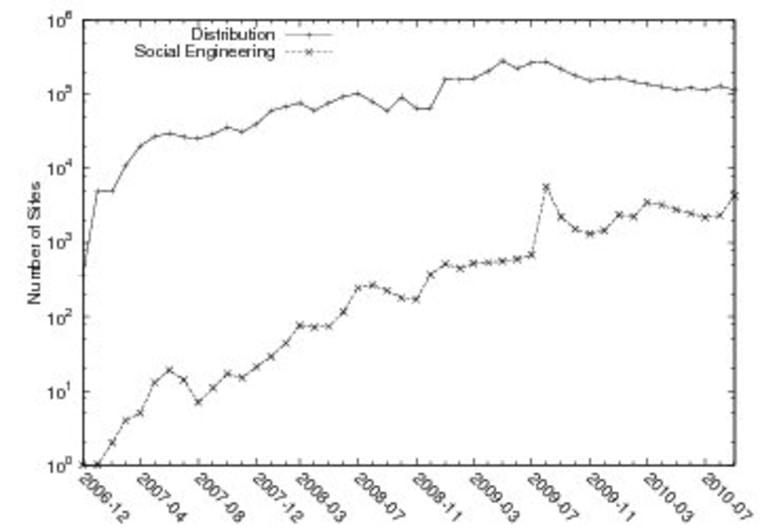
Social engineering is up, Google says. This malware distribution mechanism engages in tricking unsuspecting users into installing malware, which is usually disguised as an anti-virus product or browser plugin. But before panic sets in, the study cautions, "sites that rely on social engineering comprise only 2 percent of all sites that distribute malware."
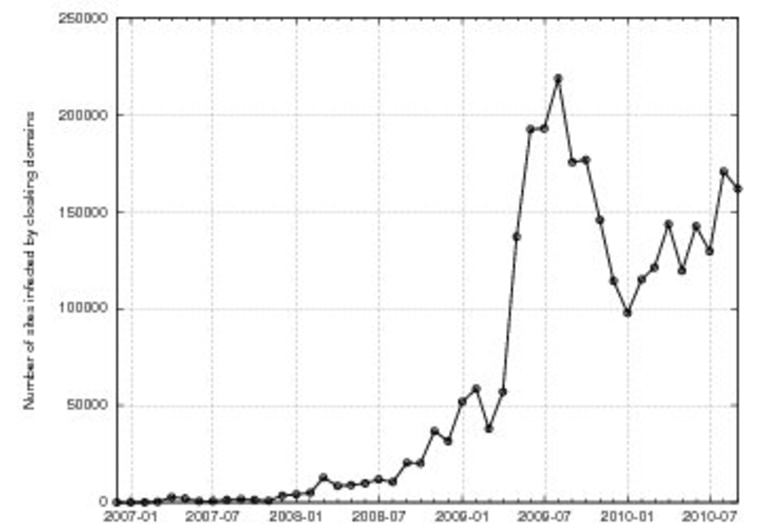
Another area where the study sees a rise in danger are drive-by downloads, which install malware after the exploit passes through a hole in a browser or plugin. IP cloaking is also another way malware distributors are getting through defenses, by showing one face (safe) to detection systems and another (malicious) to website visitors who stumble on the pages.
In this spy vs. spy world, Google is constantly trying to anticipate and outsmart its foes, which come at it from many fronts. It's a war that has only added bad guys, at least when it comes to cloaking. From 2007 through 2008, 7.21 percent of sites had only a bad reputation signal. In 2009, this jumped to 36.5 percent and last year almost reached half at 48.5 percent.
The one thing that seems to emerge from this is clear: Be vigilant. Do not open any site you think may be compromised, and don't download without scrutiny.
Google also offers these tips for users:
- Using a browser like Chrome, Firefox, or Safari that has Safe Browsing API implemented
- Keep software on their computers up-to-date with the latest versions as soon as they become available
- Run regular anti-virus scans with one or more anti-virus products.
More stories:
- Internet Explorer 9 safest Web browser?
- Google now checks your computer for malware
- Google adds downloading safety to Chrome browser
Check out Technolog on Facebook, and on Twitter, follow Athima Chansanchai, who is also trying to keep her head above water in the Google+ stream.